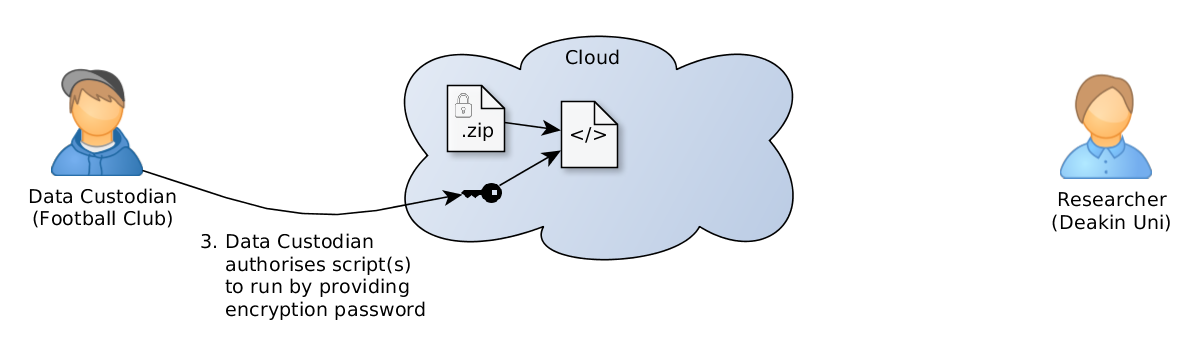
Thank you for supplying the raw data and securing the dataset with an encryption password. To ensure the data are non-identifiable to the research team (i.e. that players traces cannot be re-identified via auxiliary attributes, such as which matches the player participated in), we intend to further de-identify the data by running an automated process that extracts just the minimal data needed for the analysis. You (the data custodian) are in full control over which analyses we run, since we cannot decrypt the data without the encryption password.
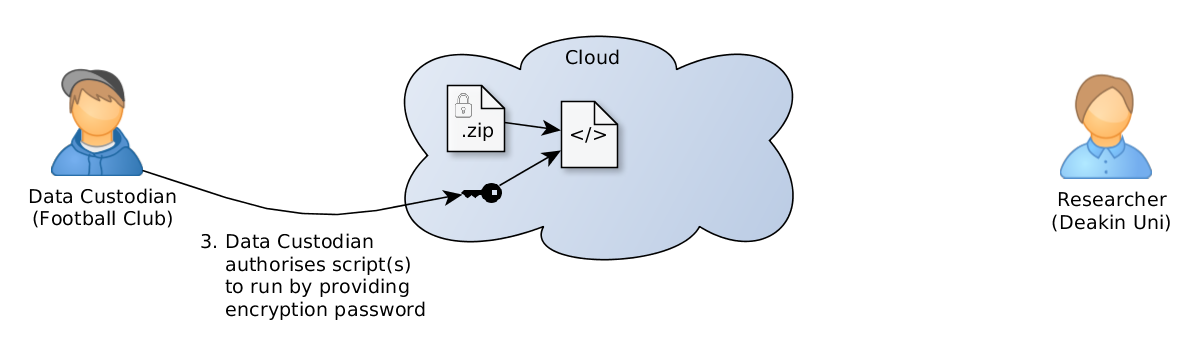
This analysis will reveal a sample of each data file to help us understand the data structure, without revealing the entire dataset.
Script: summarize_rnd.py
This analysis will extract team formations in a way that allows studying the team, but not individuals.
(For this tutorial, we will authorise the second analysis. Password used to encrypt/decrypt demo data is a2i2.)